People who follow my blog know that I am a big fan of securing Azure resources through Azure AD. Leveraging your (hopefully) well-managed organization credentials to access Azure resources, is way better than using and sharing access keys all over. You can also use Azure AD to configure password-less service-to-service authentication through the use of managed identity.
This is also true for an Azure storage account. In many scenarios, I wanted to enforce Azure AD authentication on a storage account, so I was sure that no one was using the access keys, or related Shared Access Signatures. However, this was not possible, until recently…
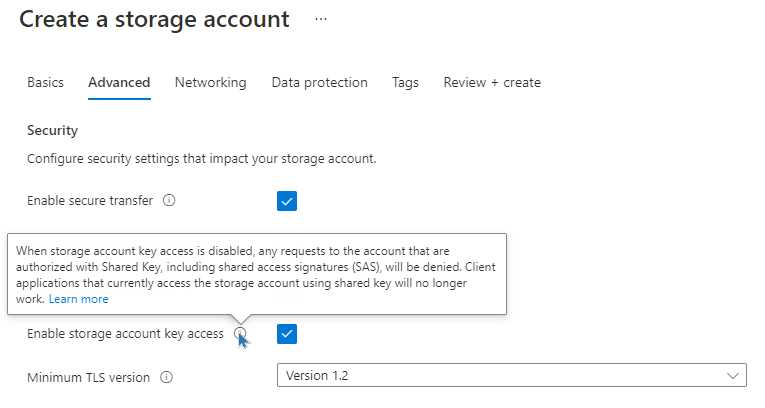
When you create a new storage account, you have now the advanced setting ‘Enable storage account key access’. Disabling this option, ensures that Azure AD authentication is enforced.
For existing storage accounts, this setting is hidden in the Configuration tab:
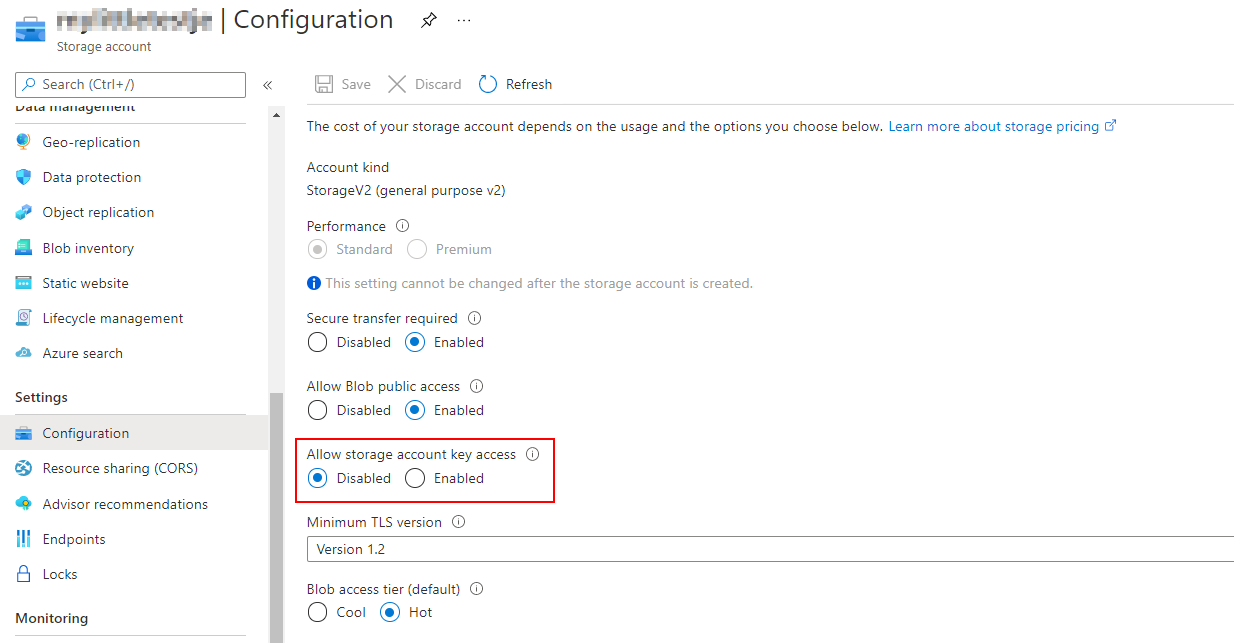
Be aware: changing this setting on existing storage accounts can have a severe impact on the running workloads. Also bear in mind that Shared Access Signature have valid use cases, so do not disable key access without reflecting first.
Cheers!
Toon












